1、對稱加密算法
對稱加密算法是應(yīng)用較早的加密算法,數(shù)據(jù)發(fā)送方將明文和密鑰經(jīng)加密算法處理,使其變成密文發(fā)送出去;接收方收到密文后,使用和加密算法相同的密鑰進(jìn)行逆算法解密,還原出明文。在對稱加密算法中,使用的密鑰只有一個(gè),收發(fā)雙方使用相同的密鑰對數(shù)據(jù)進(jìn)行加密或解密。
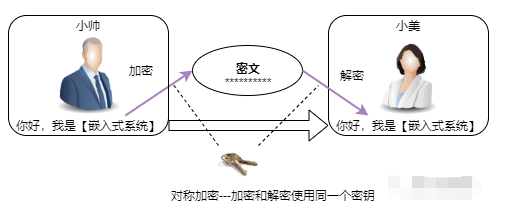
雙方都必須保管好密鑰,任一方的密鑰泄露,都會(huì)導(dǎo)致加密信息不安全;尤其是雙方協(xié)商更換密鑰過程中,密鑰會(huì)出現(xiàn)在傳輸過程中,嚴(yán)重影響數(shù)據(jù)的安全性。
對稱加密算法常用的AES可以參考[ 嵌入式算法6---AES加密/解密算法 ]
2、非對稱加密算法
和對稱加密算法最大的區(qū)別是,非對稱加密算法需要兩個(gè)密鑰,公開密鑰(public key 簡稱公鑰)和私有密鑰(private key 簡稱私鑰),且公鑰與私鑰是互相關(guān)聯(lián)的一對。使用公鑰對數(shù)據(jù)進(jìn)行加密,只有用對應(yīng)的私鑰才能解密,私鑰加密簽名也只有公鑰能解密驗(yàn)簽。
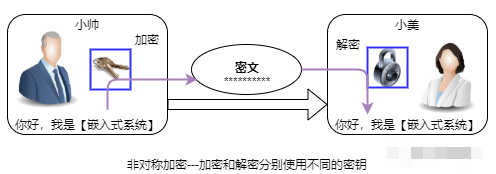
非對稱加密算法實(shí)現(xiàn)機(jī)密信息交換的基本過程:
1、甲方生成一對密鑰并將公鑰公開,私鑰保密
2、乙方使用甲方的提供的公鑰,對機(jī)密信息加密后再發(fā)送給甲方;甲方使用自己私鑰對加密后的信息進(jìn)行解密
3、甲方也可以使用自己的私鑰對機(jī)密信息進(jìn)行簽名后再發(fā)送給乙方,乙方用甲方的提供公鑰對甲方發(fā)來的密文進(jìn)行驗(yàn)簽
非對稱加密算法的特點(diǎn):
1、公鑰公開,私鑰私藏,無需雙方傳輸密鑰協(xié)商,所以安全性比對稱加密算法更高
2、非對稱加密的算法復(fù)雜,運(yùn)算速度比對稱加密解密的速度慢很多
3、一般情況下使用非對稱加密保護(hù)對稱加密的密鑰,密鑰協(xié)商后使用對稱加密進(jìn)行通信
4、最佳實(shí)現(xiàn)是雙方各自保存自己的私鑰,使用對方的公鑰加密數(shù)據(jù)傳輸
3、RSA算法與密鑰
非對稱加密算法中最常用的當(dāng)屬 RSA ,其算法本身基于一個(gè)簡單的數(shù)論知識(shí),給出兩個(gè)素?cái)?shù),很容易將它們相乘,然而給出它們的乘積,想得到這兩個(gè)素?cái)?shù)就顯得尤為困難。具體的私鑰與公鑰生成原理和加密、解密過程,不是本文關(guān)注的重點(diǎn)。
私鑰和公鑰的生成,可以借助mbedtls源碼或openSSL工具生成,舉例如下:
1、安裝openSSL,下載地址
https://www.openssl.org/
2、安裝后進(jìn)入openSSL命令行界面,使用命令生成RSA2048的私鑰,存入private.key文件
OpenSSL>genrsa -out private.key 2048
3、基于公鑰生成私鑰,存入文件public.key
OpenSSL> rsa -in private.key -pubout -out public.key
4、有些算法庫采用傳入指數(shù)、模數(shù)方式進(jìn)行加解密,而前面生成的公私鑰是PEM格式,需要變成Exponent、Modulus形式,就可以使用以下工具在線轉(zhuǎn)換。
https://www.oren.net.cn/rsa/info.html
5、關(guān)于mbedtls應(yīng)用,可以參考[ mbedtls 基礎(chǔ)及其應(yīng)用 ],該開源庫針對嵌入式系統(tǒng),且囊括了很多常用的算法。
4、源碼
以下是RSA2048的C源碼和驗(yàn)證范例,基于Qt測試,也可以結(jié)合硬件性能改為RSA1024,移植時(shí)注意適配形如 portable_***的三個(gè)API。
/************************************/
//關(guān)注微信公眾號(hào) 嵌入式系統(tǒng)
/************************************/
//rsa.h
#include "stdlib.h"
#define RSA_ENCODE_LEN (2048/8) //RSA2048即256字節(jié),可以視硬件情況改為1024
typedef unsigned char uint8_t;
typedef unsigned short int uint16_t;
typedef unsigned int uint32_t;
#define BI_MAXLEN 130
#define DEC 10
#define HEX 16
#define CARRYOVER 0x10000
#define CARRYLAST 0xFFFF
typedef struct
{
uint32_t m_nLength; //大數(shù)在0x1 00 00 00 00進(jìn)制下的長度
uint16_t m_ulValue[BI_MAXLEN]; //用數(shù)組記錄大數(shù)在0x100000000進(jìn)制下每一位的值
} CBigInt;
//rsa.c
#include "rsa.h"
#include "time.h"
/******************* 適配API *******************/
#define portable_malloc malloc
#define portable_free free
//隨機(jī)數(shù)種子源
uint32_t portable_rand_seed(void)
{
time_t timestamp;
time(×tamp);
return timestamp;
}
/******************* 適配API *******************/
/*****************************************************************
基本操作與運(yùn)算
Init, 構(gòu)造大數(shù)對象并初始化為零
Mov,賦值運(yùn)算,可賦值為大數(shù)或普通整數(shù),可重載為運(yùn)算符“=”
Cmp,比較運(yùn)算,可重載為運(yùn)算符“==”、“!=”、“>=”、“<=”等
Add,加,求大數(shù)與大數(shù)或大數(shù)與普通整數(shù)的和,可重載為運(yùn)算符“+”
Sub,減,求大數(shù)與大數(shù)或大數(shù)與普通整數(shù)的差,可重載為運(yùn)算符“-”
Mul,乘,求大數(shù)與大數(shù)或大數(shù)與普通整數(shù)的積,可重載為運(yùn)算符“*”
Div,除,求大數(shù)與大數(shù)或大數(shù)與普通整數(shù)的商,可重載為運(yùn)算符“/”
Mod,模,求大數(shù)與大數(shù)或大數(shù)與普通整數(shù)的模,可重載為運(yùn)算符“%”
*****************************************************************/
static CBigInt *Mov_Big_Long(CBigInt *X, uint32_t A);
static CBigInt *Mov_Big_Big(CBigInt *X, CBigInt *A);
static CBigInt *Add_Big_Big(CBigInt *X, CBigInt *A);
static CBigInt *Sub_Big_Big(CBigInt *X, CBigInt *A);
static CBigInt *Mul_Big_Big(CBigInt *X, CBigInt *A);
static CBigInt *Div_Big_Big(CBigInt *X, CBigInt *A);
static CBigInt *Mod_Big_Big(CBigInt *X, CBigInt *A);
static CBigInt *Add_Big_Long(CBigInt *X, uint32_t A);
static CBigInt *Sub_Big_Long(CBigInt *X, uint32_t A);
static CBigInt *Mul_Big_Long(CBigInt *X, uint32_t A);
static CBigInt *Div_Big_Long(CBigInt *X, uint32_t A);
static uint32_t Mod_Big_Long(CBigInt *N, uint32_t A);
static int Cmp(CBigInt *N, CBigInt *A);
/*****************************************************************
輸入輸出
Get,從字符串按10進(jìn)制或16進(jìn)制格式輸入到大數(shù)
Put,將大數(shù)按10進(jìn)制或16進(jìn)制格式輸出到字符串
*****************************************************************/
static CBigInt *Get(CBigInt *N, char *str, uint32_t system);
static char *Put(CBigInt *N, uint32_t system);
/*****************************************************************
RSA相關(guān)運(yùn)算
Rab,拉賓米勒算法進(jìn)行素?cái)?shù)測試
Euc,歐幾里德算法求解同余方程
RsaTrans,反復(fù)平方算法進(jìn)行冪模運(yùn)算
GetPrime,產(chǎn)生指定長度的隨機(jī)大素?cái)?shù)
*****************************************************************/
static int Rab(CBigInt *N);
static CBigInt *Euc(CBigInt *X, CBigInt *A);
static CBigInt *RsaTrans(CBigInt *X, CBigInt *A, CBigInt *B);
static CBigInt *GetPrime(CBigInt *X, int bits);
/*****************************************************************
大數(shù)運(yùn)算庫源文件:BigInt.c
說明:適用于C,linux系統(tǒng) 1024位RSA運(yùn)算
*****************************************************************/
//小素?cái)?shù)表
const static int PrimeTable[550] =
{
3, 5, 7, 11, 13, 17, 19, 23, 29, 31, 37, 41, 43, 47, 53, 59, 61, 67, 71, 73,
79, 83, 89, 97, 101, 103, 107, 109, 113, 127, 131, 137, 139, 149, 151, 157, 163, 167, 173, 179,
181, 191, 193, 197, 199, 211, 223, 227, 229, 233, 239, 241, 251, 257, 263, 269, 271, 277, 281, 283,
293, 307, 311, 313, 317, 331, 337, 347, 349, 353, 359, 367, 373, 379, 383, 389, 397, 401, 409, 419,
421, 431, 433, 439, 443, 449, 457, 461, 463, 467, 479, 487, 491, 499, 503, 509, 521, 523, 541, 547,
557, 563, 569, 571, 577, 587, 593, 599, 601, 607, 613, 617, 619, 631, 641, 643, 647, 653, 659, 661,
673, 677, 683, 691, 701, 709, 719, 727, 733, 739, 743, 751, 757, 761, 769, 773, 787, 797, 809, 811,
821, 823, 827, 829, 839, 853, 857, 859, 863, 877, 881, 883, 887, 907, 911, 919, 929, 937, 941, 947,
953, 967, 971, 977, 983, 991, 997, 1009, 1013, 1019, 1021, 1031, 1033, 1039, 1049, 1051, 1061, 1063, 1069, 1087,
1091, 1093, 1097, 1103, 1109, 1117, 1123, 1129, 1151, 1153, 1163, 1171, 1181, 1187, 1193, 1201, 1213, 1217, 1223, 1229,
1231, 1237, 1249, 1259, 1277, 1279, 1283, 1289, 1291, 1297, 1301, 1303, 1307, 1319, 1321, 1327, 1361, 1367, 1373, 1381,
1399, 1409, 1423, 1427, 1429, 1433, 1439, 1447, 1451, 1453, 1459, 1471, 1481, 1483, 1487, 1489, 1493, 1499, 1511, 1523,
1531, 1543, 1549, 1553, 1559, 1567, 1571, 1579, 1583, 1597, 1601, 1607, 1609, 1613, 1619, 1621, 1627, 1637, 1657, 1663,
1667, 1669, 1693, 1697, 1699, 1709, 1721, 1723, 1733, 1741, 1747, 1753, 1759, 1777, 1783, 1787, 1789, 1801, 1811, 1823,
1831, 1847, 1861, 1867, 1871, 1873, 1877, 1879, 1889, 1901, 1907, 1913, 1931, 1933, 1949, 1951, 1973, 1979, 1987, 1993,
1997, 1999, 2003, 2011, 2017, 2027, 2029, 2039, 2053, 2063, 2069, 2081, 2083, 2087, 2089, 2099, 2111, 2113, 2129, 2131,
2137, 2141, 2143, 2153, 2161, 2179, 2203, 2207, 2213, 2221, 2237, 2239, 2243, 2251, 2267, 2269, 2273, 2281, 2287, 2293,
2297, 2309, 2311, 2333, 2339, 2341, 2347, 2351, 2357, 2371, 2377, 2381, 2383, 2389, 2393, 2399, 2411, 2417, 2423, 2437,
2441, 2447, 2459, 2467, 2473, 2477, 2503, 2521, 2531, 2539, 2543, 2549, 2551, 2557, 2579, 2591, 2593, 2609, 2617, 2621,
2633, 2647, 2657, 2659, 2663, 2671, 2677, 2683, 2687, 2689, 2693, 2699, 2707, 2711, 2713, 2719, 2729, 2731, 2741, 2749,
2753, 2767, 2777, 2789, 2791, 2797, 2801, 2803, 2819, 2833, 2837, 2843, 2851, 2857, 2861, 2879, 2887, 2897, 2903, 2909,
2917, 2927, 2939, 2953, 2957, 2963, 2969, 2971, 2999, 3001, 3011, 3019, 3023, 3037, 3041, 3049, 3061, 3067, 3079, 3083,
3089, 3109, 3119, 3121, 3137, 3163, 3167, 3169, 3181, 3187, 3191, 3203, 3209, 3217, 3221, 3229, 3251, 3253, 3257, 3259,
3271, 3299, 3301, 3307, 3313, 3319, 3323, 3329, 3331, 3343, 3347, 3359, 3361, 3371, 3373, 3389, 3391, 3407, 3413, 3433,
3449, 3457, 3461, 3463, 3467, 3469, 3491, 3499, 3511, 3517, 3527, 3529, 3533, 3539, 3541, 3547, 3557, 3559, 3571, 3581,
3583, 3593, 3607, 3613, 3617, 3623, 3631, 3637, 3643, 3659, 3671, 3673, 3677, 3691, 3697, 3701, 3709, 3719, 3727, 3733,
3739, 3761, 3767, 3769, 3779, 3793, 3797, 3803, 3821, 3823, 3833, 3847, 3851, 3853, 3863, 3877, 3881, 3889, 3907, 3911,
3917, 3919, 3923, 3929, 3931, 3943, 3947, 3967, 3989, 4001
};
/****************************************************************************************
大數(shù)比較
調(diào)用方式:Cmp(N,A)
返回值:若N5、應(yīng)用
和AES一樣,RSA也是塊加密算法( block cipher algorithm),只針對固定長度數(shù)據(jù)塊,如RSA2048其加密的數(shù)據(jù)長度需要填充后是2048位即256字節(jié),如果明文長度大于244字節(jié)則需要拆分。當(dāng)然最簡單的辦法是應(yīng)用層分配多個(gè)244字節(jié)緩存,有效數(shù)據(jù)以外以0x00填充。
RSA算法雖然安全,但其計(jì)算量非常大,效率較低,尤其在嵌入式系統(tǒng)中,硬件資源有限的情況下加密、解密時(shí)間以秒為單位。而對稱加密算法AES算法效率高,但其在密鑰協(xié)商時(shí),在網(wǎng)絡(luò)傳輸中有被攔截的風(fēng)險(xiǎn),或者任一方保存不當(dāng)導(dǎo)致密鑰泄露,其密鑰存在很大的安全隱患。
所以,考慮到安全性和高效性,一般采用多種算法組合加密的方式。使用RSA來加密AES的密鑰,密鑰協(xié)商后,使用AES來對后續(xù)數(shù)據(jù)進(jìn)行加密。
更多信息,請關(guān)注微信公眾號(hào) 嵌入式系統(tǒng)
-
數(shù)據(jù)
+關(guān)注
關(guān)注
8文章
7002瀏覽量
88942 -
密鑰
+關(guān)注
關(guān)注
1文章
138瀏覽量
19753 -
加密算法
+關(guān)注
關(guān)注
0文章
215瀏覽量
25541
發(fā)布評(píng)論請先 登錄
相關(guān)推薦
RSA加密算法
加密算法(DES,AES,RSA,MD5,SHA1,Base64)
地圖數(shù)據(jù)網(wǎng)絡(luò)分發(fā)的混合加密算法
常見公鑰加密算法有哪些
什么是非對稱加密?非對稱加密概念

java實(shí)現(xiàn)非對稱加密算法的過程



 嵌入式的RSA非對稱加密算法
嵌入式的RSA非對稱加密算法









評(píng)論